So I recently stumbled upon a problem with building Imagick PHP extension on CentOS/RHEL 7 and it drove me a little bit mad co’z I can’t seem to find the fix only to realize that the solution was actually so easy.
Building Imagick PHP extension for CentOS/RHEL 7 fails with error `C preprocessor “/lib/cpp” fails sanity check` and how to fix it
06 Jan 2017 Leave a comment
in DevOps, Software, Web Development Tags: centos, GCC, ImageMagick, Imagick, Linux, php, php extension, rhel
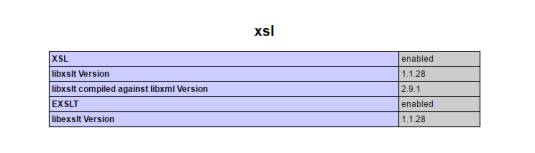
Installing PHP XSL extension on CentOS 7
17 Dec 2016 2 Comments
in DevOps, Software, Web Development Tags: centos, centos7, Linux, php, php extension, php-xsl, sysadmin, xsl
So you just finished installing php and then tried deploying your app, but then you are greeted with something like:
. . . the requested PHP extension xsl is missing from your system. . .
or
. . . requires PHP XSLT extension. Please enable it first then. . .
Don’t despair because installing and enabling this extension on CentOS 7 is a piece of cake!
Git-Jenkins CI using Vagrant and Docker
10 Dec 2016 Leave a comment
in DevOps, Web Development Tags: cd, ci, continuous delivery, continuous integration, DevOps, docker, git, github, jenkins, nodejs, vagrant
Did you ever feel bored doing the same repetitive tasks over and over again such as testing and deploying code changes? Many of us developers and sysadmins experience this same scenario and if you don’t know a way to get around this, your productivity is probably very low. Fortunately, computers doesn’t feel bored doing the same things over and over. So, let’s make them do the boring stuff while we focus on the interesting ones.
Virtualizing Drupal Development Environment with Vagrant, Drush & Co
13 Nov 2015 Leave a comment
in DevOps, Web Development Tags: ansible, drupal, drush, vagrant, virtual development environment, virtualbox
This post is a rip-off of my presentation from the last DrupalCamp Cebu entitled Virtualizing Drupal Development Environment. If you want to check some info of that presentation including the slides, please go here. All codes shown here are available on my GitHub repo drupal-vm.
GHOST Vulnerability: CVE-2015-0235
29 Jan 2015 1 Comment
in Software, Technology Tags: CVE-2015-0235, ghost, glibc, Linux, vulnerability
Background Information:
Last January 27, 2015, cloud security provider Qualys announced a vulnerability in all versions of the GNU C library (glibc).
Details:
According to RedHat’s CVE Database:
A heap-based buffer overflow was found in glibc's __nss_hostname_digits_dots() function, which is used by the gethostbyname() and gethostbyname2() glibc function calls. A remote attacker able to make an application call either of these functions could use this flaw to execute arbitrary code with the permissions of the user running the application.

Fresh Crappy Comments